Edwards & The CMMC Ecosystem
Edwards plays a role in nearly every aspect of the Cybersecurity Maturity Model Certification (CMMC) ecosystem — training and education, consulting, assessments, and certification. Currently, Edwards supports Organizations Seeking Certification (OSC) as a Registered Practitioner Organization (RPO) and authorized CMMC Third-Party Assessment Organization (C3PAO), providing The Cyber AB approved assessments, consulting, and audit preparation. We are also a Licensed Training Provider (LTP) and Licensed Partner Publisher (LPP), developing training and providing The Cyber AB certified classes to organizations and individuals planning to take The Cyber AB certification exams or utilize LPP curriculum. Check out our CMMC FAQ page for more in-depth answers to all your CMMC questions!
Our team of cybersecurity experts bring more than a half century’s worth of deep understanding and experience in assessing and interpreting standards, guidelines, and best practices to improve cybersecurity programs. These skills provide you with a diverse and knowledgeable team, making us the best choice for your CMMC needs.
Assessments
Edwards is an Authorized CMMC Third-Party Assessment Organization (C3PAO) with Certified CMMC Assessors on staff, ready to support your formal CMMC assessment. Contact Info@EdwPS.com today!
Consulting
Edwards is an RPO, but more importantly, our consultants are also CMMC Provisional Assessors. In fact, many of our consultants teach our CCP classes and developed our curriculum. Learn more.
Education
As an LPP, Edwards developed the curriculum to train the assessment community using cybersecurity SMEs and ISDs. Our courses prepare individuals to do the job an OSC expects when they hire a CMMC Professional.
Training
As an LTP, Edwards uses our own renowned curriculum to train members of the OSC team, consultants, supporting organizations (e.g., MSPs), and of course the assessors themselves. View our courses.
The Cybersecurity Maturity Model Certification (CMMC 2.0) is a unified standard for implementing cybersecurity across the defense industrial base. While the CMMC Standard was created for the Defense Supply Chain, there are many other government agencies and allies of the United States interested in using the CMMC Standard.
The standard is overseen by The Cyber AB. The Cyber AB establishes and oversees a qualified, trained, and high-fidelity community of consultants and assessors who can deliver consistent and informative assessments to participating organizations against a defined set of controls/best practices within the CMMC Program. The CMMC 2.0 Model itself is created and managed by both The Cyber AB and the DoD. CMMC is designed to:
• Safeguard sensitive information to enable and protect the warfighter
• Dynamically enhance DIB cybersecurity to meet evolving threats
• Ensure accountability while minimizing barriers to compliance with DoD requirements
• Contribute toward instilling a collaborative culture of cybersecurity and cyber resilience
• Maintain public trust through high professional and ethical standards
The CMMC 2.0 Model
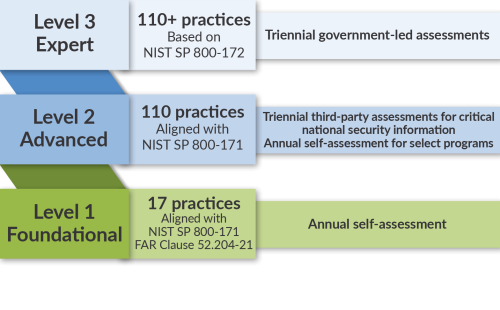
The CMMC will review and combine various cybersecurity standards and best practices and map these controls and processes across several maturity levels that range from basic cyber hygiene to advanced. The level of certification an organization requires is largely dependent on the type of information they handle and the work they may be bidding.
CMMC will start to appear in upcoming statements of work once federal rule-making is complete (estimated 9-24 months; August 2022-November 2023), and it is critical to prepare for compliance now. High formal assessment demand means you must be prepared to pass the first time or risk being waitlisted – potentially foregoing large DoD contract opportunities. CMMC compliance will be a go-no-go decision gate at the time of the contract award.
CMMC QUICK FACTS
✅ CMMC draws from NIST standards, the DoD, and the international security community; CMMC 2.0 focuses entirely on NIST 800-171 security safeguards
✅ One size does not fit all – different levels of security are necessary, depending on the contract and sensitivity of the data involved
✅ CMMC 2.0 won’t appear in contracts until rulemaking is decided (As of Tuesday 12/26 the CMMC proposed rule is out and “published” meaning that the 60-day public comment period has begun and CMMC is one step closer to being implemented.)
✅ CMMC includes the entire DoD industrial base – approximately 300,000 contractors and subcontractors
✅ The Cyber AB LPPs and LTPs are authorized to develop and train OSCs in various CMMC certification and informational courses
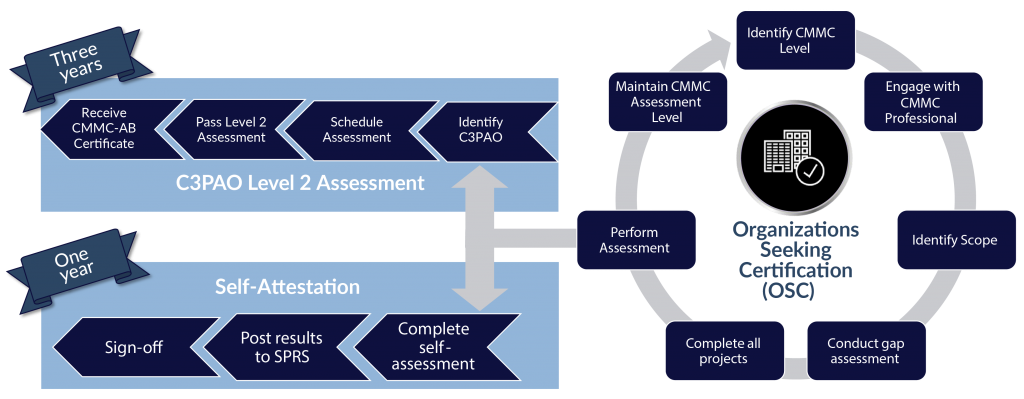
Working towards self-attestation or formal certification within the CMMC ecosystem can be a daunting task for any organization. This is where the need for various training and education can make a world of difference in understanding the CMMC Model, best practices, and the ability to apply concepts around protecting information. It is critical to have a solid comprehension of the legal and regulatory guidance as it pertains to the Department of Defense’s (DoD) Cybersecurity posture.
As The Cyber AB’s Licensed Partner Publisher (LPP) and Licensed Training Provider (LTP), Edwards produces quality training materials for other LTPs or Organizations Seeking Certification (OSC).
The Cyber AB’s Approved Training Materials (CATM) are developed by internal and external CMMC cybersecurity rockstars who bring a dynamic blend of real-world NIST assessment and consulting experience. Our highly sought-after CMMC courses and boot camps are taught by our team of world-class Provisional Instructors – the industry’s most respected CMMC experts. It is no surprise that the quality and professionalism of our curricula set the bar in the CMMC training ecosystem, as our courses are created using Edwards’ instructional systems design approach based on industry standards – and have been for 23+ years.
Our online courses and accompanying course materials are updated continuously to provide the most accurate and recent CMMC information, but if live certification boot camps are not a right fit for you we offer a Guided Learning option, SME-led CMMC peer groups, and ongoing study groups. We aim to provide flexible learning at the click of a button – delivering an accessible way to enhance and develop CMMC expertise. We also offer customized training and discounts for multiple seat purchases; inquire to learn more!
The Cyber AB COURSES ARE IN Session!
Your CMMC certification journey begins with a solid foundation. The Cyber AB-approved 5-day CCP course and the Guided Learning CCP course provide a comprehensive look at the CMMC 2.0 standard and prepares participants to perform as effective CMMC assessors, implementers, and consultants. With our team of world-class Provisional Instructors with decades of experience, participants can expect a well-rounded view of CMMC. The 5-day CCA course builds on your knowledge of the CMMC model, taking the perspective of an actual assessment using multiple scenario OSC environments varying in size, locations, and on-prem vs. hybrid systems. This course prepares you for the CCA exam and for your role on a C3PAO assessment team or as a consultant to successfully lead an organization in their Level 2 CMMC Assessment.
Enroll in a session today or contact us to book a private class!
To continue work with the government, organizations will be required to either self-attest to 800-171 safeguards at Level 1/Level2, or must be certified at CMMC Maturity Level 2 or Level 3 depending on contract requirements, but most aren’t sure where to start. The Cyber AB created the RPO certification to provide OSCs confidence in their consultant selection for both quality and knowledge of CMMC concepts to get the job done. C3PAOs are the only organizations authorized to conduct official CMMC assessments against security practices of Maturity Level 1 or Level 2 designated by The Cyber AB. If your government contract requires Level 3, a C3PAO will be required to assess and recommend a Level 2 award prior to a DIBCAC Level 3 assessment.
As an RPO and C3PAO, Edwards is equipped to provide advisory CMMC Level 1 or Level 2 consulting services and support, as well as pre-certification assessments to establish a CMMC plan of action. OSCs should work with an RPO or C3PAO to prepare for either certification; however, you cannot engage with the same C3PAO for both pre-assessment consulting services and the actual CMMC assessment. All verified RPOs and C3PAOs are listed on The Cyber AB Marketplace. Our goal is to advise DoD suppliers on how to best prepare for a successful CMMC assessment and enforce the maturity levels designed by The Cyber AB.
Our team of cybersecurity experts brings more than a half century’s worth of understanding and experience in assessing and interpreting standards, guidelines, and best practices to improve cybersecurity programs. Edwards has actively conducted NIST 800-171 assessments since 2015, and as an organization was an early entrant into the CMMC ecosystem. Edwards is here to assist you on your CMMC journey!
CMMC PREPARATION
Our targeted, yet simple, approach delivers big results that respect your budget, timeline, and inform key stakeholders. Each engagement is tailored to the needs of your business. We partner with you to ensure readiness for the formal CMMC assessment process. Where weaknesses or gaps are found, we develop goal-oriented, impactful action plans that support compliance and also positively impact your business.
At this time, Edwards offers CMMC Level 1 facilitated self-assessments. We help organizations determine their Supplier Performance Risk System (SPRS) score by evaluating your systems against the NIST 800-171 framework. We also offer CMMC Level 2 preparation assessments. Regardless of the engagement, Edwards offers varying levels of consulting support, including data flow diagramming, scoping, full-scale gap assessment, remediation planning and road mapping (i.e., POAMs), and remediation support. Edwards continues to increase our offerings as the DoD provides more CMMC compliance information. Contact us at Info@EdwPS.com for more information.
Our Cybersecurity Team brings more than ten decades of combined cybersecurity experience in assessing and interpreting NIST, CIS, HIPAA and ISO 27001 standards and guidelines. Our expert management and implementation of security programs throughout the government, commercial, and healthcare industries is well respected and far reaching. Meet our team by hovering over their name!

Sam Bell
Chief Information Security Officer
PMP ⚬ SSCP ⚬ RP

Matt Hoeper
Sr. Cybersecurity Consultant & Solution Lead
PMP ⚬ CISSP ⚬ CCA ⚬ CCP ⚬ PA ⚬ PI

Marcellus Williams
Sr. Penetration Tester
CEH Master ⚬ Security+ ⚬ CCNA ⚬ CISSP ⚬ GPEN

Joe Stoner
Cybersecurity Consultant
CEH ⚬ CySA+ ⚬ CCP

Tyler Gormus
Cybersecurity Consultant
CEH ⚬ CCP ⚬ PA

Rebecca Duve
Cybersecurity Project Manager
PMP ⚬ PMI-ACP ⚬ Security+
Want More?
Check out our other solutions – Enterprise Management, IT Solutions, Training & Development, and Cybersecurity.
INTERESTED IN MORE CMMC RESOURCES?
Learn to meet cybersecurity business goals and organizational priorities, while connecting with the best in the business.